

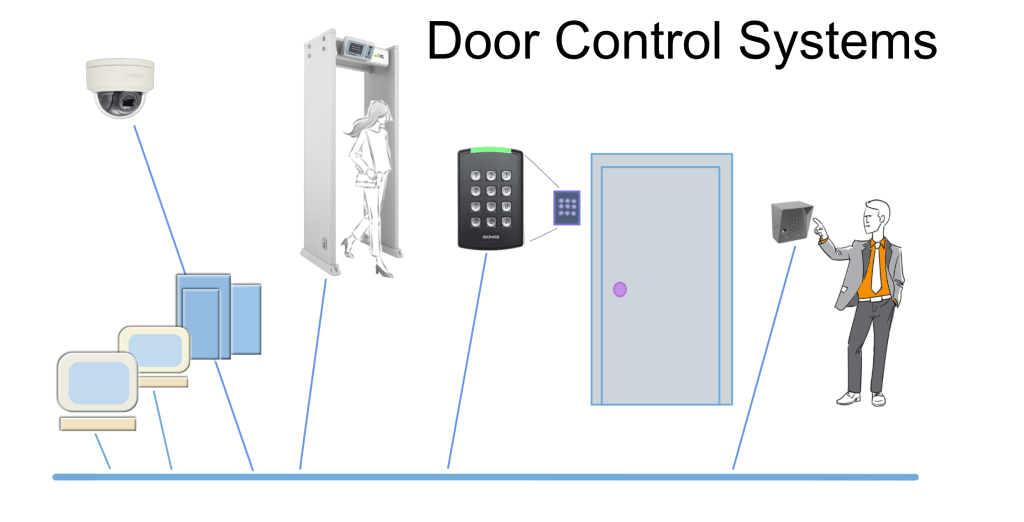
Access control system provides security by giving flexible control over who is allowed to enter your premises. Access control system is one of the most common used system in electronic door control using a card or a magnetic stripe which can be accessed by swiping through a reader on the door. These access control systems are used for security purposes.
The areas or organizations which require high security use different types of access control systems like bio metric, RFID, door controllers and card readers etc. Each access point may be controlled individually as per the requirement of company or organizations where high security is necessary. Network security is also important, especially in a company which handles sensitive data.
By this card access control systems allows access to enter into the premises limiting people to one side of the door. In some cases, physical access control systems are integrated with electronic ones by limiting the users allowing them to utilize the resources limited on a computer system.
To secure a facility, organizations use electronic access control systems that rely on user credentials, access card readers, auditing and reports to track employee access to restricted business locations and proprietary areas, such as data centers. Some of these systems incorporate access control panels to restrict entry to rooms and buildings as well as alarms and lock-down capabilities to prevent unauthorized access or operations.
Access control systems perform identification authentication and authorization of users and entities by evaluating required login credentials that can include passwords, personal identification numbers (PINs), bio-metric scans, security tokens or other authentication factors. Multi-factor authentication, which requires two or more authentication factors, is often an important part of layered defense to protect access control syste
Also known as Rule-Based Access Control, RBAC is the most demanded in regard to access control systems. Not only is it in high demand among households, RBAC has also become highly sought-after in the business world. In RBAC systems, access is assigned by the system administrator and is stringently based on the subject’s role within the household or organization and most privileges are based on the limitations defined by their job responsibilities.
So, rather than assigning an individual as a security manager, the security manager position already has access control permissions assigned to it. RBAC makes life much easier because rather than assigning multiple individuals particular access, the system administrator only has to assign access to specific job titles.
This access control mechanism restricts access to computer resources based on individuals or groups with defined business functions — executive level, engineer level 1 — rather than the identities of individual users. The role-based security model relies on a complex structure of role assignments, role authorizations and role permissions developed using role engineering to regulate employee access to systems. RBAC systems can be used to enforce MAC and DAC frameworks.
When this paradigm is used, permissions are granted according to roles and roles are assigned to users. This model is user-friendly because administrators can centrally manage and administer roles.
An access control method in which owners or administrators of the protected system, data or resource set the policies defining who or what is authorized to access the resource. Many of these systems enable administrators to limit the propagation of access rights. A common criticism of DAC systems is a lack of centralized control.
Discretionary Access Control is a type of access control system that holds the business owner responsible for deciding which people are allowed in a specific location, physically or digitally. DAC is the least restrictive compared to the other systems, as it essentially allows an individual complete control over any objects they own, as well as the programs associated with those objects. The drawback to Discretionary Access Control is the fact that it gives the end user complete control to set security level settings for other users and the permissions given to the end user are inherited into other programs they use which could potentially lead to malware being executed without the end user being aware of it.
The user has direct control over all of the programs and files in the system, which is a complicated way of saying one method of access always opens all the doors.
This is the opposite of DAC. When MAC is the paradigm, a policy, hardware component, or software component is used to restrict access. This can be a password or keypad.
Mandatory Access Control is more commonly utilized in organizations that require an elevated emphasis on the confidentiality and classification of data (ie. military institutions). MAC doesn’t permit owners to have a say in the entities having access in a unit or facility, instead, only the owner and custodian have the management of the access controls. MAC will typically classify all end users and provide them with labels which permit them to gain access through security with established security guidelines.
A security model in which access rights are regulated by a central authority based on multiple levels of security. Often used in government and military environments, classifications are assigned to system resources and the operating system or security kernel, grants or denies access to those resource objects based on the information security clearance of the user or device. For example, Security Enhanced Linux is an implementation of MAC on the Linux operating system.

Protect your facilities with a range of options. We can erect K-rated fences and gates, pop-up barriers, traffic barricades and more. We can also customize a solution to ensure proper flow at a single or multiple entry points.

We offer complete electronic access services. We can design, build, implement and support a customized system that protects and also provides invaluable data on who entered and left your facility and the times of day it occurred.

Biometrics is an advanced security system with a variety of ways to let people access your facility or areas within it. We can install systems that scan a fingerprint, iris, face or other means of identification. Biometrics eliminates the need for card access and can integrate with existing access systems.

We can manage your access control so you can focus on what you do best – your business. We provide a complete turnkey solution, which includes installation, service and support as well as weekly or monthly reports, software upgrades, alarm reporting, employee permissions, holiday scheduling and more.

Imagine being able to monitor your entire facility from a web browser offsite. With hosted access control, it’s all possible. A customized hosted access system allows you to manage permissions in real time, network multiple facilities at once and remove the need for software and IT maintenance.

Armed Forces

Sports

Accomodations

Storage
Contact us today to request for inspection of your facility and quotation for installation…